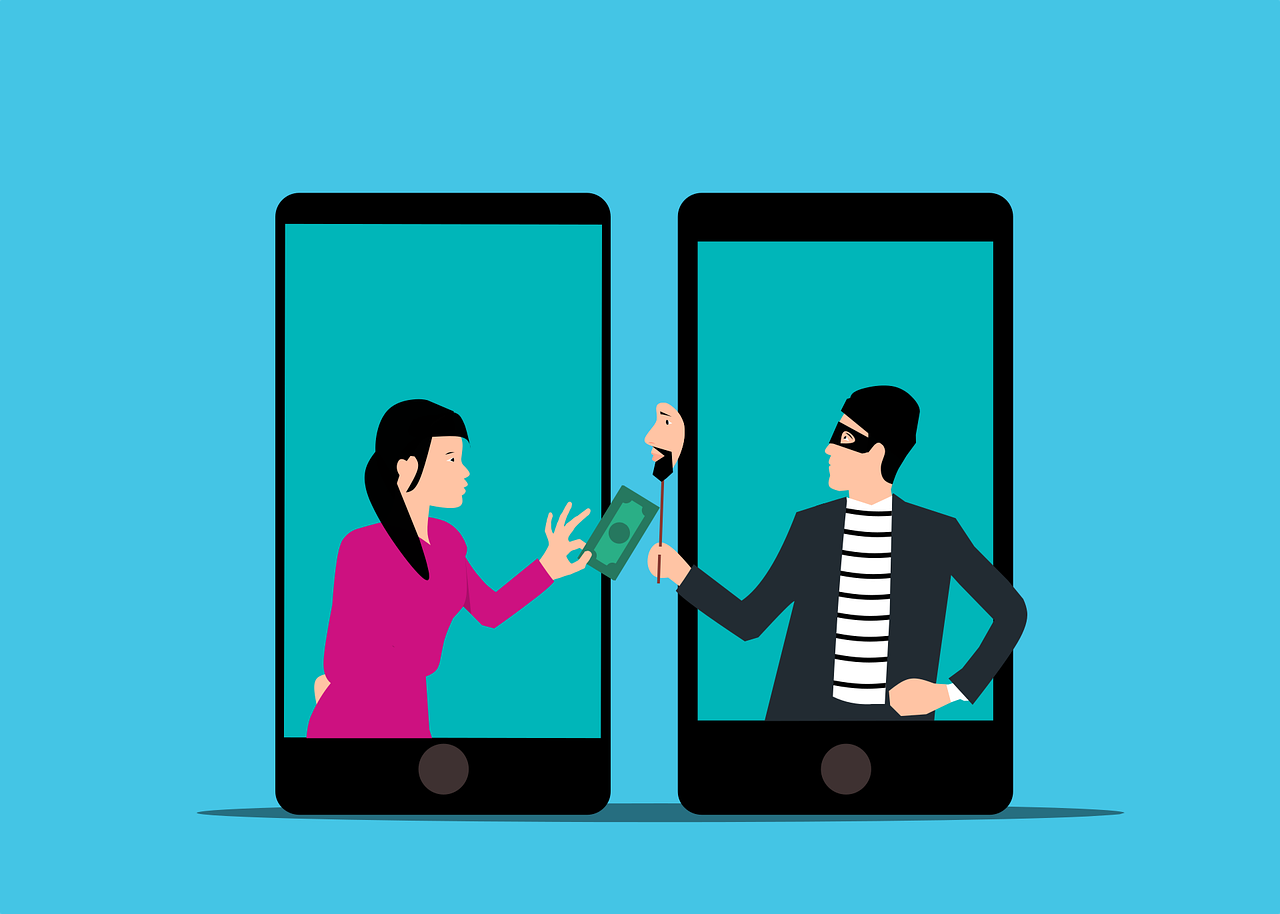
Is That Really a Text from Your CEO… or Is It a Scam?
Imagine you’re going about your day when suddenly you receive a text from the CEO. The head of the company is asking for your help. They’re out doing customer visits and someone else dropped the ball in providing gift cards. The CEO needs you to buy six $200 gift cards and text the information right [...]